The Windows Defender Credential Guard, also known as Microsoft Defender Credential Guard, is a security feature in the Windows and Windows Server operating systems. Although it is there to make your credentials secure, some users are experiencing problems with it.
Some have reported that due to this feature, the Remote Desktop Connection now consistently asks for credentials, while others are experiencing problems running the VMWare hypervisor.
In this article, we are going to address what Windows Defender Credential Guard is, and how can you disable it, or enable it, if needed.
Table of Contents
What is Windows Defender Credential Guard
The Credential Guard is part of Windows Security that was first introduced in Windows 10 Enterprise edition, which has now also been carried forward to Windows 11 Professional edition, amongst others.
The Windows Defender Credential Guard uses virtualization technology to isolate your credentials so that they cannot be stolen via unauthorized access. This feature prevents hackers from accessing vulnerable data and credential theft attacks, and only authorized systems can view or edit them.
It is because of this reason that users experience repeated credentials windows when trying to access remote computers via RDP.
In Windows 10, this feature is disabled by default but is automatically enabled when you enable Hyper-V. In Windows 11 Pro, this feature is enabled by default, provided that your system meets the minimum requirements.
Here is a list of the minimum hardware and software requirements for Credential Guard to be enabled:
- Support for Virtualization-based security
- Secure boot
- Trusted Platform Module (TPM) versions 1.2 or 2.0
- UEFI lock (preferred)
- 64-bit CPU
- CPU virtualization
- Windows hypervisor (does not require Hyper-V Windows Feature to be installed)
Below you’ll find the methods to enable Windows Defender Credential Guard or disable it in case it is causing.
The Credential Guard can be seen inside Windows Security inside “Device Security” under Core Isolation. However, there is no option to configure it.
Credential Guard can be enabled or disabled using Group Policy and the Windows Registry. However, in Windows 10, the method to enable it requires an additional step.
We have discussed the methods in detail below.
Disable Windows Defender Credential Guard in Windows 10
In Windows 10, the Credential Guard is automatically enabled when you enable Hyper-V, In the method below, we will show you how to disable Credential Guard while Hyper-V is still enabled.
To disable Credential Guard in Windows 10, we must first enable Hyper-V.
Enable Hyper-V
Open the Optional Features applet by typing in “optionalfeatures” in the Run Command box.

Open the Optional Features applet Select “Hyper-V” and click Ok.

Enable Hyper-V The wizard will now install Hyper-V and its components.
When installed, close the wizard.

Close the wizard
Now, it is time to disable Credential Guard. This can be done via the Group Policy.
Disable Credential Guard
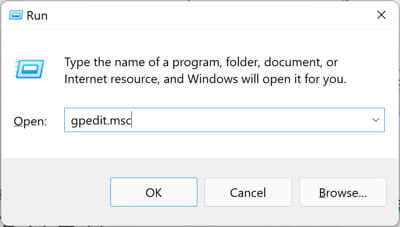
Open the Group Policy editor by typing in “gpedit.msc” in the Run Command box.
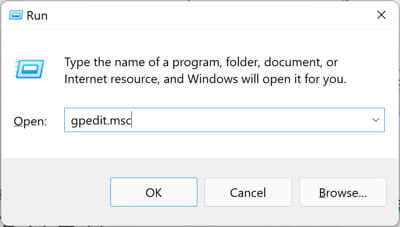
Open the Group Policy editor Navigate to the following from the left pane:
Local Computer Policy >> Computer Configuration >> Administrative Templates >> System >> Device Guard
Double-click the policy “Turn On Virtualization Based Security.”

Edit VBS policy Select “Disabled,” then click Apply and Ok.

Disable the VBS policy Now run the following cmdlet in an elevated Command Prompt for the changes to take effect.
GPUpdate /Force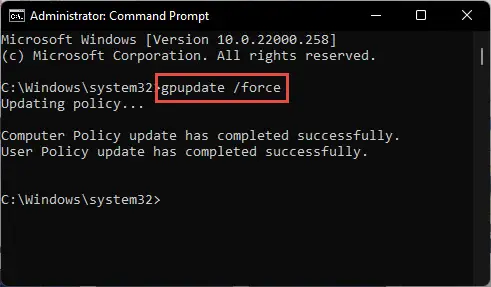
Enforce the Group Policies
The Windows Defender Credential Guard will now be disabled with the Hyper-V enabled.
However, if you wish to enable Credential Guard on Windows 10, follow the guide in the next section below.
Enable Windows Defender Credential Guard in Windows 10
To enable the Credential Guard in Windows 10, follow these steps:
First, enable Hyper-V as given in the method above.
Now open the Group Policy editor and navigate to the following:
Local Computer Policy >> Computer Configuration >> Administrative Templates >> System >> Device Guard
Double-click the policy “Turn On Virtualization Based Security.”

Edit policy Select “Enabled.”
Under the Options section, select the following settings from the drop-down menus:
Select Platform Security Level:
- Secure Boot and DMA Protection
Virtualization Based Protection of Code Integrity:
- Enabled with UEFI Lock – So the option cannot be disabled remotely, or
- Enabled without lock – Windows Defender Credential Guard can be disabled remotely.
Credential Guard Configuration:
- Enabled with UEFI Lock – So the option cannot be disabled remotely, or
- Enabled without lock – Windows Defender Credential Guard can be disabled remotely.
Secure Launch Configuration:
- Not Configured – If you choose it to be configured by your domain administrator, or
- Enabled – If you want to turn on Secure Launch, or
- Disabled – If you want to disable Secure Launch

Configure VBS to enable Credential Guard in Windows 10 Click Apply and Ok.
Now run the following cmdlet in an elevated Command Prompt for the changes to take effect.
GPUpdate /Force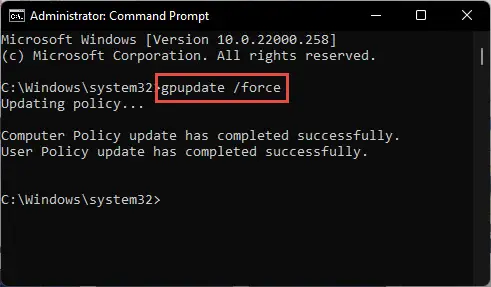
Enforce Group Policies
Windows Defender Credential Guard will now be enabled.
There are also other methods to disable or enable the Credential Guard in Windows 10. The following methods also apply to Windows 11.
Disable Windows Defender Credential Guard in Windows 11 using Group Policy
As mentioned earlier, the Credential Guard is enabled by default in Windows 11. You can disable it using the Windows Group Policy editor, and through Windows Registry. You can use any of the following given methods to disable it or re-enable it if needed.
Follow these steps to disable the Credential Guard in Windows 11 or Windows 10 using the Group Policy editor:
Open the Group Policy editor by typing in “gpedit.msc” in the Run Command box.
Open the Group Policy editor Navigate to the following from the left pane:
Local Computer Policy >> Computer Configuration >> Administrative Templates >> System >> Device Guard
Double-click the policy “Turn On Virtualization Based Security.”

Edit VBS policy Select “Disabled,” then click Apply and Ok.

Disable the VBS policy Now run the following cmdlet in an elevated Command Prompt for the changes to take effect.
GPUpdate /Force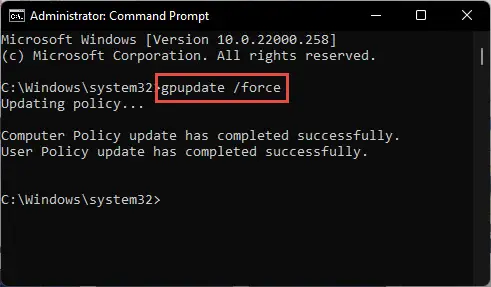
Enforce the Group Policies
The Windows Defender Credential guard will now be disabled. However, to enable it, perform the steps in the next section.
Enable Windows Defender Credential Guard in Windows 11 using Group Policy
Open the Group Policy editor and navigate to the following:
Local Computer Policy >> Computer Configuration >> Administrative Templates >> System >> Device Guard
Double-click the policy “Turn On Virtualization Based Security.”

Edit policy Select “Enabled.”
Under the Options section, select the following settings from the drop-down menus:
Select Platform Security Level:
- Secure Boot and DMA Protection
Virtualization Based Protection of Code Integrity:
- Enabled with UEFI Lock – So the option cannot be disabled remotely, or
- Enabled without lock – Windows Defender Credential Guard can be disabled remotely.
Credential Guard Configuration:
- Enabled with UEFI Lock – So the option cannot be disabled remotely, or
- Enabled without lock – Windows Defender Credential Guard can be disabled remotely.
Secure Launch Configuration:
- Not Configured – If you choose it to be configured by your domain administrator, or
- Enabled – If you want to turn on Secure Launch, or
- Disabled – If you want to disable Secure Launch
(Windows 11 22H2) Kernel-mode Hardware-enforced Stack Protection:
- Disabled – Turns off kernel-mode Hardware-enforced Stack Protection, or
- Enabled in audit mode – enables kernel-mode Hardware-enforced Stack Protection where shadow stack violations are not fatal and will be logged to the system event log, or
- Enabled in enforcement mode – enables kernel-mode Hardware-enforced Stack Protection where shadow stack violations are fatal, or
- Not Configured – leaves the policy setting undefined

Configure VBS to enable Credential Guard in Windows 11 Click Apply and Ok.
Now run the following cmdlet in an elevated Command Prompt for the changes to take effect.
GPUpdate /Force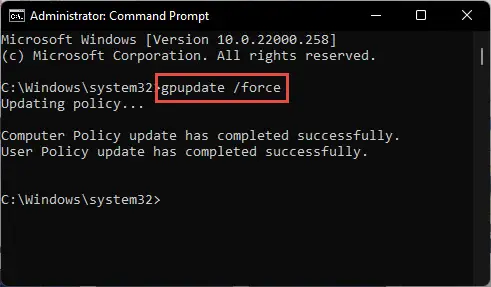
Enforce Group Policies
Windows Defender Credential Guard will now be enabled.
You can also enable or disable the Credential Guard from Windows Registry.
Disable Windows Defender Credential Guard in Windows 11/10 from Windows Registry
If you are unable to disable the Windows Defender Credential Guard using the Group Policy editor, then you can use the Registry editor to get the job done. Here are the steps to disable the Credential Guard from Windows Registry:
Note: Misconfiguration of critical values in the system’s registry could be fatal for your operating system. Therefore, we insist that you create a system restore point before proceeding forward with the process.
You can also use our top selection of disk imaging and backup software so you never lose your data or operating system again.
Open the Registry Editor by typing in “regedit” in the Run Command box.
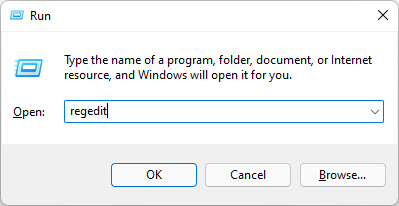
Open the Registry Editor Paste the following in the navigation bar for quick navigation and press Enter:
Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\DeviceGuard

Navigate to DeviceGuard Create a new DWORD and name it “EnableVirtualizationBasedSecurity”.

Create DWORD EnableVirtualizationBasedSecurity Right-click the DeviceGuard key, expand New, then click “DWORD (32-bit) Value,” and name this key “EnableVirtualizationBasedSecurity.”
Note: If this or any other value inside the Windows Registry already exists, then do not create a new one. Instead, perform the following action on the existing Registry.
Double-click the DWORD “EnableVirtualizationBasedSecurity” and set its Value Data to “0.”

Set Value Data for EnableVirtualizationBasedSecurity Now paste the following in the navigation bar to change the directory:
Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa

Navigate to Lsa Create a new DWORD named “LsaCfgFlags.”
Set the Value Data for “LsaCfgFlags” to “0.”

Set Value Data for LsaCfgFlags Restart the computer for the changes to take effect.
When the computer restarts, you will find that the Windows Defender Credential Guard has been disabled.
Enable Windows Defender Credential Guard in Windows 11/10 from Windows Registry
If you want to enable Windows Defender Credential Guard from Windows Registry, then follow these steps. Note that these steps are a little different from the ones given above to disable the feature, as it involves an additional Registry value.
Open the Registry Editor by typing in “regedit” in the Run Command box.
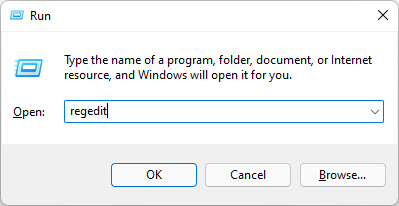
Open the Registry Editor Paste the following in the navigation bar for quick navigation and press Enter:
Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\DeviceGuard

Navigate to DeviceGuard Create a new DWORD and name it “EnableVirtualizationBasedSecurity”.

Create DWORD EnableVirtualizationBasedSecurity Right-click the DeviceGuard key, expand New, then click “DWORD (32-bit) Value,” and name this key “EnableVirtualizationBasedSecurity.”
Note: If this or any other value inside the Windows Registry already exists, then do not create a new one. Instead, perform the action on the existing Registry.
Double-click the DWORD “EnableVirtualizationBasedSecurity” and set its Value Data to “1.”

Set Value Data for EnableVirtualizationBasedSecurity Create another DWORD within the same “DeviceGuard” key and name it “RequirePlatformSecurityFeatures”.
Set the Value Data for “RequirePlatformSecurityFeatures” to “1.”

Set Value Data for RequirePlatformSecurityFeatures Now paste the following in the navigation bar to change the directory:
Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa

Navigate to Lsa Create a new DWORD named “LsaCfgFlags.”
Set the Value Data for “LsaCfgFlags” to “1.”

Set Value Data for LsaCfgFlags Restart the computer for the changes to take effect.
Windows Defender Credential Guard will now be enabled. This method can be adopted on both Windows 10 and Windows 11, as long as your PC meets the requirements.
How to Check if Windows Defender Credential Guard is Enabled or Disabled
Whether you have made changes to enable or disabled the Credential Guard, or just want to check its status, there are methods you can try.
From System Information
Open the System Information applet by typing in “msinfo32” in the Run Command box.

Open System Information Stay in the “System Summary” tab.
On the right side, look for the value in front of “Virtualization-based security Services Running.”

Check System Information for Credential Guard status If the value says “Credential Guard,” it means that Credential Guard is activated and running.
Using Windows PowerShell
Simply run the following cmdlet in an elevated PowerShell instance to check the current status of Credential Guard:
(Get-CimInstance -ClassName Win32_DeviceGuard -Namespace root\Microsoft\Windows\DeviceGuard).SecurityServicesRunning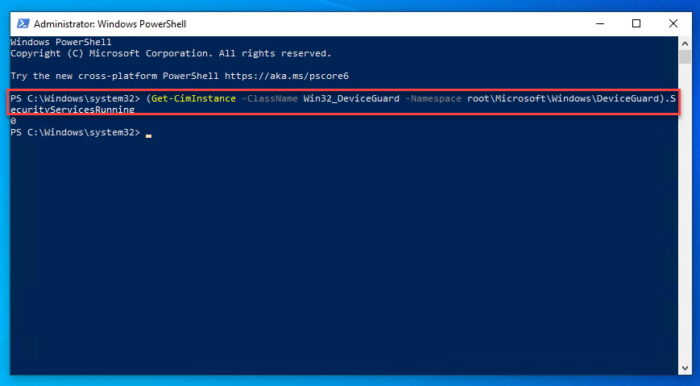
One of the following outputs would then be generated, informing you of whether Windows Defender Credential Guard is running or not:
- 0 – Credential Guard is disabled
- 1 – Credential Guard is enabled
Closing Thoughts
The Windows Defender Credential Guard ought to be running at all times. It keeps your usernames and passwords safe from hackers.
However, if it causes any trouble, such as issues with VMWare, or the fact that you are annoyed by the constant credentials prompts, you can always disable it.
That said, we still recommend that you re-enable it once you are done with your work.
The methods to enable and disable Windows Defender Credential Guard are given in this post for both Windows 10 and 11 and can be done from the Group Policy Editor and the Registry Editor.