Microsoft has released its Security Baseline for the recently-launched Windows 11 22H2 operating system. You can download and install the Security Baseline using the guide provided down below.
A Security Baseline is an additional set of security enhancements that can be added to the original security protocols already in place in Windows. This is especially useful for companies and organizations that prefer to take more control of their virtual security.
If you are a system administrator, installing a Security Baseline on a Windows 11 computer will add additional options to the Group Policy so you can control and push those settings to other devices on the entire network.
Table of Contents
Download Windows 11 v22H2 Security Baseline
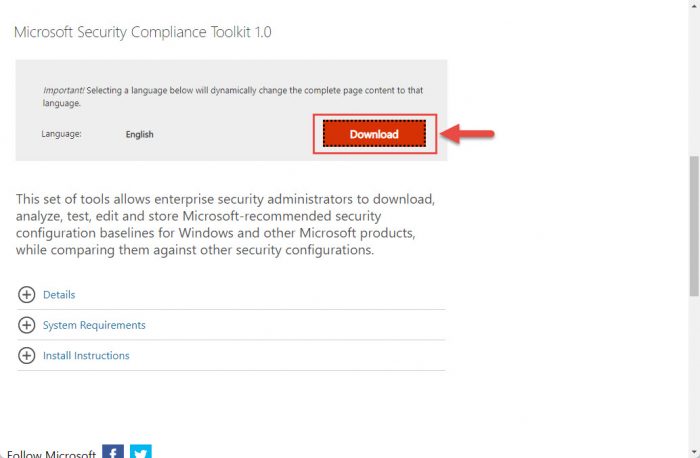
The Windows 11 Security Baseline has been released as a component of Microsoft Security Compliance Toolkit 1.0. Even so, you can download only the security baseline. Here are the steps to do so:
-
Open the Microsoft Security Compliance Toolkit page and click Download.
Download -
Check the box next to “Windows 11 version 22H2 Security Baseline.zip” and click Next.

Select and proceed -
Windows 11 22H2 Security Baseline will now download. Since it is only 1.4 MB, it should be downloaded instantly. Once downloaded, extract the content of the zip file to a folder.
-
Now navigate to the extracted folder and open the Scripts sub-folder. Here you will find 3 PowerShell ISE files. Right-click each of those files one after the other and then click Run with PowerShell from the context menu.
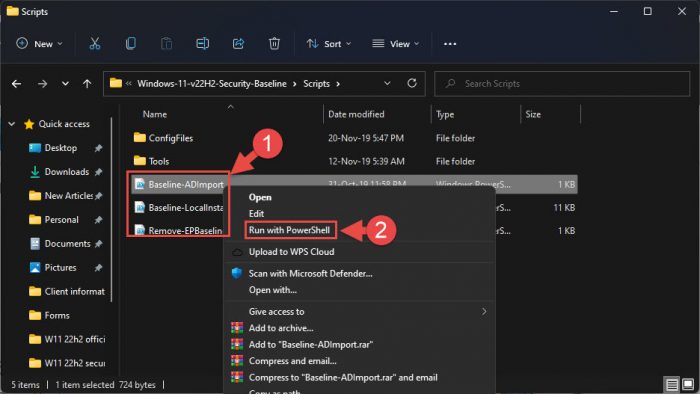
Run scripts with PowerShell The scripts will now run automatically. Wait for the PowerShell window to close on its own.
Once all 3 files are executed via Windows PowerShell, Windows 11 22H2 Security Baseline will be installed successfully.
Let us now see what changes this baseline introduces for Windows 11.
New in Windows 11 22H2 Security Baseline
Kernel Mode Hardware Enforced Stack Protection
This new feature has been added to Windows 11 version 22H2 and above that will protect your hardware from automatic and unauthorized exploits by preventing arbitrary code execution.
This configuration can be found at the following location inside Group Policy:
Computer Configuration >> Administrative Templates >> System >> Device Guard >> Turn on Virtualization Based Security
To learn more about the Kernal Mode Hardware Enforced Stack Protection feature, refer to this guide post.
Enhanced Phishing Protection
This security baseline adds several features to ensure that a Windows username and password cannot be used for malicious purposes on an enterprise network. The following list of security enhancements has been made:
-
The security baseline enforces enablement of the service (the Service Enabled setting) to ensure that the enterprise credentials used in the system are appropriately monitored and audited.
Based on Microsoft Defender SmartScreen’s robust security infrastructure, when a user enters their credentials into a known phishing or malicious site, the service alerts the user. In this scenario, the setting Notify Malicious is set to Enabled.

Unsafe connection prompt. Source: Microsoft -
Should a user re-use their corporate credentials in another application or website, a notification is displayed and logged. In this scenario, the setting Notify Password Reuse is set to Enabled.

Notification of password reuse. Source: Microsoft -
Should a user decide to save their passwords in Notepad, WordPad, or other Office applications, this activity is logged with Microsoft Defender for Endpoint and the user is notified of the activity. In this scenario, the setting Notify Unsafe App is set to Enabled.
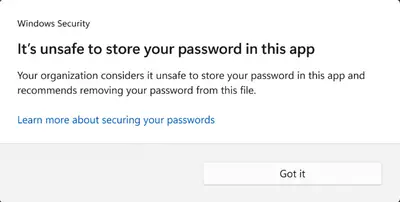
Notification of unsafe password storage. Source: Microsoft
You can enable or disable this feature at the following location inside Group Policies:
Computer Configuration >> Administrative Templates >> Windows Components >> Windows Defender SmartScreen >> Enhanced Phishing Protection
Enhanced Printer Security
Some new settings have been implemented with Windows 11 22H2 security baseline that will keep all communications with a printer safe inside an enterprise network:
- Support for RedirectionGuard is added to the print service. RedirectionGuard is a security measure that prevents the use of non-administratively created redirection primitives from being followed within a given process. The setting Configure Redirection Guard is now Enabled as part of the baseline.
- Historically, Named Pipes were allowed with Print Spoolers. The use of TCP for the settings Configure RPC connection and Configure RPC listener is now enforced.
- Configure RPC over TCP port ensures that the incoming and outgoing connections default to a dynamic TCP port.
These additional settings can be found at the following location:
Computer Configuration >> Administrative Templates >> Printers
Other Security Enhancements
Several other new security enhancements have also been incorporated in Windows 11 22H2 security baseline:
- Enterprises can now configure DNS over HTTPS.
- The “Configure NetBIOS settings” will be now enabled by default.
- Improvements have been made to enhance credential theft protection.
- The attack surface has been reduced by blocking abuse of exploited vulnerable signed drivers.
- Addition of account lockout policies.
You can read more about these improvements in the Windows 11 22H2 Security Baseline Release Notes.
Closing Words
With every feature OS update, Microsoft releases a new security baseline so that enterprises can secure their systems as per their needs. Similarly, the Windows 11 22H2 security baseline was released alongside Windows 11 2022 Update so that when the enterprise systems update to the latest version, their computers are not left vulnerable to exploits.
We highly recommend that you download and install Windows 11 22H2 Security Baseline regardless if you are a sysadmin or a private user. It will allow you to enhance your digital security and give you more control over it.
