Computer users often only use and require a handful of applications, depending on their type of work and usage. For example, a computer installed at a doctor’s reception desk may only need to run a few Microsoft Office apps and maybe a scheduling software. Thus, all others can be disabled.
Thankfully, Windows 11, Windows 10, and a few Server editions come with a built-in app called “AppLocker.” As the name suggests, this utility is used to lock away applications that you do not want the users to use. This can be done if you want to revoke access to authoritative apps, or simply prevent your employees from wasting time on things they should not be doing while at work.
If you are looking for a native solution to block certain apps and programs on a computer, let us show you how.
Table of Contents
What is AppLocker
AppLocker is a built-in utility for some Microsoft products, including some Windows and Server editions. It is used to control which apps and programs can run on your system, including executable (.exe) files, scripts, Windows Installer files, packaged applications (Microsoft Store apps), etc.
AppLocker is used to define rules that allow or block the .exe or the .com files associated with the app. By default, since there are no rules configured, all applications are allowed to run normally. Below you will find a table that explains the default AppLocker rules:
| Purpose | Name | Group | Path |
|---|---|---|---|
| Allow members of the local Administrators group access to run all executable files | (Default Rule) All files | BUILTIN\Administrators | All |
| Allow all users to run executable files in the Windows folder | (Default Rule) All files located in the Windows folder | Everyone | %windir%* |
| Allow all users to run executable files in the Program Files folder | (Default Rule) All files located in the Program Files folder | Everyone | %programfiles%* |
However, if you create an exception for one app, all others are blocked unless you make an exception for them too. Microsoft explains this in the following statement:
If no AppLocker rules for a specific rule collection exist, all files with that file format are allowed to run. However, when an AppLocker rule for a specific rule collection is created, only the files explicitly allowed in a rule are permitted to run.
Microsoft
With that said, there are additional steps you can take to mitigate the issue of all other applications being automatically blocked when creating a new rule in the AppLocker. This has been discussed in the steps given below to block an app.
How to Use AppLocker to Block Executable Files/Apps
Below is a step-by-step guide to configuring AppLocker to block an application from running on a computer:
Note: This method uses the Local Security Policy/ Group Policy Editor, which is not available in Windows Home editions by default. Learn how to enable the Group Policy Editor or the Local Security Policy Editor in Windows Home.
- First, we need to ensure that the “Application Identity” service is up and running. This service is responsible for enforcing the AppLocker policies. To do so, open the Command Prompt with administrative privileges and enter the following cmdlet:
sc config "AppIDSvc" start=auto & net start "AppIDSvc"
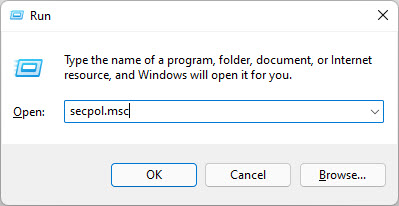
Note: This cmdlet will also configure the service to automatically startup when Windows boots. - Now close the Command prompt and open the Local Security Policy Editor by typing in secpol.msc in Run.
- Here, expand Application Control Policies and then AppLocker from the left pane.

Note: This can also be done using the Group Policy Editor. Open it up by typing in gpedit.msc in Run, then navigate to the following using the left pane:Computer Configuration >> Windows Settings >> Security Settings >> Application Control Policies >> AppLocker
The next steps remain constant.
- Click AppLocker from the left pane, and then click Configure Rule Enforcement on the right.

- From the AppLocker properties window, check the box next to Configured under Executable rules and then click OK.

- Now, go back to the Local Security Policy editor and click “Packaged App Rules” under AppLocker on the left pane.

- Now right-click “Packaged App Rules” and click Create default rules from the context menu.

Note: This step is essential as AppLocker will block all Microsoft Store applications from running. This step will set the default rules for all apps, which allows all applications to run. - Now click “Executable Rules” in the left pane. Then, right-click on it and select Create default rules from the context menu.

Note: Not performing this step automatically blocks all applications from running, except for the ones explicitly allowed. - Right-click “Executable Rules” again, and now click Create New Rules from the context menu.

- The wizard to create rules will now launch. On the first page, click Next.

- Now select Deny, and then click Select to choose a user or group to apply the rule for. When selected, click Next.

- Select Path and click Next.

- Now click either of the following buttons and select either a file or a folder to block, respectively. Selecting a folder will block all executables from running inside of it. When selected, click Next.
- On the next page, leave the default values and click Next.

- Now enter a custom name for the rule and click Create.

You will now see that the rule has been added to the AppLocker.

You can now repeat steps 9 through 15 to add more apps or folders to block.
If you wish to allow an app or an entire folder again, simply navigate to the same location within the Local Security Policy/Group Policy Editor and delete the associated rules.

Once the rule has been created, a user who is trying to access the blocked content will see the following prompt:
This app has been blocked by your system administrator. Contact your system administrator for more info.

Closing Words
AppLocker is for those people who do not wish to use third-party applications but want to control which applications are used on their or their employee’s computers. Not only will it prevent other people from doing the tasks they are not permitted to do, but blocking apps that provide administrative rights to users will also enhance your overall security.